
Tales from the Real World - Azure AD B2C: A real silver bullet
When COVID-19 forced the vOpen.Tech conference to pivot from a physical event to a fully virtual one, the organising team had fewer than two weeks to build a production-ready registration and identity system — with minimal budget. In this episode, Chris is joined by Facundo La Rocca (Faku), a .NET developer and conference organiser from Buenos Aires, Argentina, who shares how Azure AD B2C became the silver bullet that made it possible.
Before the pandemic, vOpen.Tech used Eventbrite for registration alongside on-site barcode scanning and paper-based data collection. Going virtual exposed a critical gap: Eventbrite could not capture the custom attendee information the team needed — seniority level, technologies in use, years of experience, spoken languages — and there was no equivalent on-site mechanism in a virtual world.
Faku walks through the journey from problem statement to production:
- Why Azure AD B2C: The decision to reach for Azure AD B2C over building a custom identity solution from scratch, highlighting the service’s support for custom user attributes, user flows, and social identity provider integration.
- Custom user attributes: Azure AD B2C’s extensible directory model allowed the team to capture exactly the audience data they needed without custom backend development.
- Under two weeks delivery: With minimal code, no dedicated budget, and a tight deadline, the team went from zero to a production-ready, scalable, secure identity and registration platform for an entire conference.
- Zero cost at scale: Azure AD B2C’s free tier covers 5,000 monthly active users per account — the conference ran entirely at no cost, with no infrastructure management overhead.
- Key advice: If you need to build something around authentication and authorisation, give Azure AD B2C a try before writing your own. The service is production-ready, scalable, and battle-tested — it is rarely worth starting from scratch.
This episode is a compelling illustration of how a well-chosen PaaS identity service can unlock solutions that would otherwise be out of reach for small teams and community-driven projects.
Related Content

12 - Modern Identity Patterns
Chris is joined by Christos Matskas — former Microsoft Premier Field Engineer, developer tools evangelist, and .NET identity expert — for a deep-dive into modern identity patterns in the cloud. They cut through the confusion between Azure AD, Azure AD B2B, Azure AD B2C, and External Identities, explain why the network perimeter is no longer your security boundary, and make the case for letting battle-hardened libraries like MSAL do the heavy lifting rather than rolling your own auth. From eliminating secrets in ARM templates to Zero Trust principles, this episode lays a practical foundation for securing any cloud application.
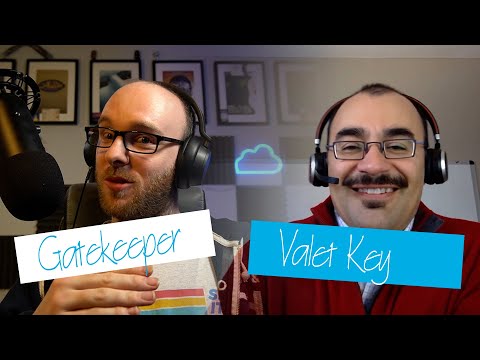
23 - Gatekeeper and Valet Key Patterns - Secure your APIs and Resources
Continuing the 'Architecting for the Cloud, one pattern at a time' series, Chris and Peter Piper explore two closely related cloud design patterns for securing APIs and backend resources. The Gatekeeper pattern positions a dedicated host between untrusted clients and trusted backend services — handling authentication, authorization, request validation, protocol translation, and rate limiting. The Valet Key pattern complements it by issuing short-lived, scope-restricted tokens (such as Azure SAS tokens) so clients can access specific resources directly, reducing load on central services without sacrificing security. The episode covers practical implementation options on Azure including API Management, Azure Key Vault, and Azure App Configuration.

V028 - Weekly Technology Vlog #28
Chris returns from vacation with Azure, DevOps, and GitHub updates covering resilience threat modeling, Azure Well-Architected Framework reliability, Privileged Identity Management with Azure Lighthouse, App Service Environment v3, and Azure Communication Services direct routing.